[ad_1]
A North Korea-aligned activity cluster tracked by ESET as DeceptiveDevelopment drains victims’ crypto wallets and steals their login details from web browsers and password managers
20 Feb 2025
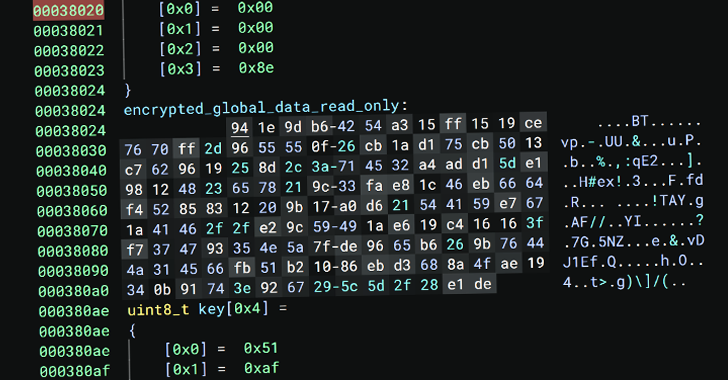
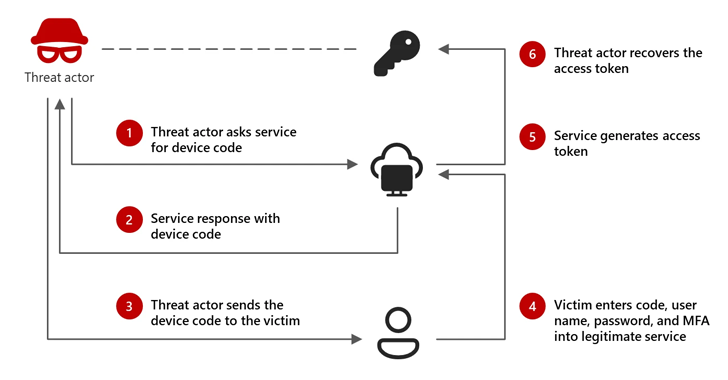
ESET researchers have observed a malicious campaign where North Korea-aligned threat actors, posing as headhunters, target freelance software developers with info-stealing malware.
The activities – named DeceptiveDevelopment and going back to at least November 2023 – involve spearphishing messages that are being distributed on job-hunting and freelancing sites and ask the targets to take a coding test, with the files necessary for the task usually hosted on private repositories such as GitHub. These files are laden with malware, however, which ultimately lets the attackers steal the victims’ login details and drain their cryptocurrency wallets.
What else is there to know about the campaign’s tactics, techniques, and procedures? Learn from ESET Chief Security Evangelist Tony Anscombe in the video and make sure to read the full blogpost.
Connect with us on Facebook, X, LinkedIn and Instagram.
[ad_2]
Source link